rktchip adrianhand Thank you for raising here this request/concern. There are several AMD CPUs affected and (at least) two different vulnerabilities, so likely multiple Beelink models are also affected.
- AMD-SB-7033 - AMD CPU Microcode Signature Verification Vulnerability – affects AMD CPUs with Zen 1 up to Zen 5
- AMD-SB-7055 - RDSEED Failure on AMD “Zen 5” Processors – affects AMD CPUs with Zen 5 only
On both cases they require proper CPU microcode (uCode) updates with the latest patched AGESA™ (AMD Generic Encapsulated System Architecture) versions, readily available from AMD, to be deployed on BIOS/UEFI updates by the OEM mainboard manufacturers. 👉 That means you @Beelink!
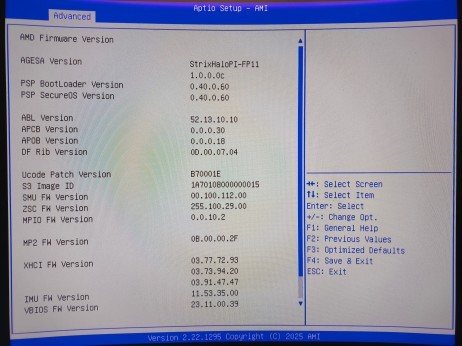
Specifically, on my GTR9 Pro model with the AMD Ryzen AI Max+ 395 cpu with the latest BIOS/UEFI version P110 I confirmed that it is still using very old unpatched AGESA version StrixHaloPI-FP11 1.0.0.0c and old microcode (uCode) version 0x0b70001e .
These unpatched AGESA and microcode versions and existing RDSEED vulnerability (and mitigation) can also be confirmed on Linux terminal with:
$ sudo dmesg | grep microcode
[ 0.523280] microcode: Current revision: 0x0b70001e
$ sudo dmesg | grep RDSEED32
[ 0.135120] RDSEED32 is broken. Disabling the corresponding CPUID bit.
⚠️ But we know that the latest microcode (uCode) update available from AMD for the AMD Ryzen AI Max+ 395 (family: 0x1a, model: 0x70, stepping: 0x0) cpu is 0x0b700032. But on the GTR9 Pro we are all on the older unpatched 0x0b70001e.
👉 @Beelink Please provide BIOS/UEFI updates with the latest patched AGESA and microcode (uCode) updates for the several models affected. 🙏